If you are searching for LDAP NITRR, you are probably trying to understand what LDAP is and how it works in real-world networks.
LDAP stands for Lightweight Directory Access Protocol. It is a powerful authentication protocol used to access and manage directory services over a network. Today, most companies rely on LDAP for centralized login systems, user authentication, and access control.
In this complete guide, we will explain LDAP Nitrr in simple language so that beginners, IT students, and cybersecurity learners can understand it clearly.
Table of Contents
What Is LDAP?
LDAP (Lightweight Directory Access Protocol) is an open standard protocol that allows applications to access and maintain distributed directory information services.
In simple terms, LDAP helps organizations store and manage:
- Usernames
- Passwords
- Employee records
- Email addresses
- Devices
- Security permissions
When someone logs into a corporate system, the credentials are verified through an LDAP server. If the details match, the user gets access.
That is why LDAP Nitrr is commonly searched by students learning about network authentication and enterprise security.
What Is a Directory Service?
A directory service is a centralized database designed to store and retrieve information efficiently.
Unlike traditional databases, directory services are optimized for:
- Fast searches
- Read-heavy operations
- Structured hierarchical data
LDAP is the protocol that allows systems to communicate with the directory.
One of the most popular implementations of LDAP is:
Active Directory is widely used in Windows environments for managing users, computers, and policies.
How LDAP Works
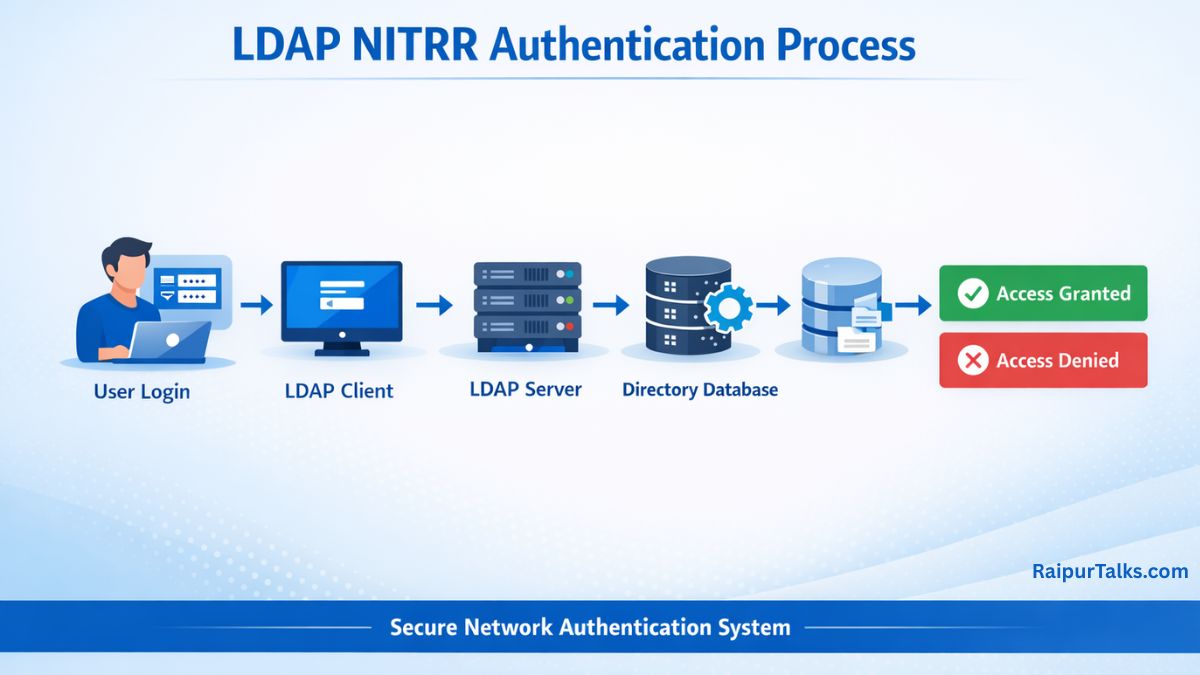
To understand LDAP Nitrr properly, you need to understand how LDAP works step by step.
1. Client Sends Request
An application (email server, VPN, or login system) sends a request to the LDAP server.
2. Authentication
The LDAP server verifies the username and password.
3. Directory Search
If authentication is successful, the server searches the directory tree.
4. Response
The server returns the requested information.
This process happens within milliseconds in most enterprise networks.
LDAP Architecture Explained
LDAP follows a hierarchical structure similar to a tree.
Example structure:
dc=company,dc=com
└── ou=Users
└── cn=John Doe
Here:
- dc = Domain Component
- ou = Organizational Unit
- cn = Common Name
This structure makes LDAP highly organized and efficient.
That is why LDAP Nitrr is important in structured enterprise environments.
LDAP Ports and Security
LDAP works on specific network ports:
- Port 389 → Default LDAP
- Port 636 → Secure LDAP (LDAPS)
LDAPS uses SSL/TLS encryption, which improves network security. In modern environments, secure LDAP is strongly recommended.
Without encryption, LDAP traffic can be intercepted, which may expose sensitive credentials.
Why LDAP Is Important in Enterprises
Many organizations depend on LDAP because it provides:
Centralized Authentication
All user accounts are stored in one place.
Single Sign-On (SSO)
Users log in once and access multiple systems.
Access Control
Permissions can be managed efficiently.
Scalability
LDAP supports thousands of users easily.
Because of these features, LDAP Nitrr is relevant for IT infrastructure and cybersecurity students.
LDAP vs Active Directory
Many people confuse LDAP with Active Directory.
Here is the difference:
- LDAP → A protocol
- Active Directory → A directory service that uses LDAP
Active Directory also uses other technologies like Kerberos and DNS, but LDAP is a core component.
So when someone searches for LDAP Nitrr, they often want to understand how LDAP connects with Active Directory systems.
LDAP in Cybersecurity and Ethical Hacking
LDAP is also important in penetration testing.
Security professionals test LDAP configurations for:
- Anonymous binds vulnerabilities
- Weak passwords
- Misconfigured permissions
- Data leakage
If LDAP is not secured properly, attackers may extract user information.
That is why secure configuration of LDAP servers is critical for network security.
Real-World Example of LDAP Usage
Imagine a company with 1,000 employees.
Without LDAP:
- Each computer would store separate login data.
- Managing users would be chaotic.
With LDAP:
- All users are managed centrally.
- Password changes apply everywhere.
- Access control is easier.
This is why LDAP Nitrr becomes important for understanding enterprise IT systems.
Advantages of LDAP
Here are some key advantages:
- Lightweight and fast
- Open standard protocol
- Cross-platform support
- Centralized management
- High performance for searches
Because of these benefits, LDAP remains widely used even today.
Disadvantages of LDAP
Although LDAP is powerful, it has some limitations:
- Complex initial setup
- Requires proper security configuration
- Needs encryption (LDAPS) for safe communication
However, with correct implementation, LDAP is highly reliable.
Frequently Asked Questions About LDAP NITRR
What does LDAP stand for?
LDAP stands for Lightweight Directory Access Protocol.
Is LDAP secure?
LDAP itself is not encrypted. However, LDAPS (LDAP over SSL/TLS) provides secure communication.
Is LDAP the same as Active Directory?
No. LDAP is a protocol, while Active Directory is a directory service that uses LDAP.
Where is LDAP used?
LDAP is used in enterprise authentication systems, VPNs, email servers, cloud applications, and network security management.
Official LDAP NITRR Portal (ldap.nitrr.ac.in)
If you are searching for LDAP Nitrr, you are most likely looking for the official login portal of the National Institute of Technology Raipur.
The official website is:
This portal is used by students and staff for LDAP authentication and academic access management.
What is ldap.nitrr.ac.in?
The website ldap.nitrr.ac.in is the official LDAP authentication system of NIT Raipur. It allows users to log in using their institutional credentials.
The portal is mainly used for:
- Student login authentication
- Institutional email generation
- Password reset and account recovery
- Internet access authentication
- Academic and administrative account management
Because the domain directly matches the keyword LDAP Nitrr, Google ranks it at the top position for login-related searches.
However, this portal is strictly for authorized NITRR students and staff members only.
Final Thoughts on LDAP NITRR
Understanding LDAP Nitrr is essential if you are learning about networking, cybersecurity, or enterprise IT infrastructure.
LDAP plays a crucial role in authentication, directory services, and centralized user management. It enables organizations to maintain security, efficiency, and scalability.
Whether you are an IT student or a professional, learning how LDAP works will give you a strong foundation in network architecture and authentication systems.